SD-WAN security: How to protect your network + checklist
11 minute read time
Organizations have become more reliant on systems and technologies that operate outside of an official office structure. From an enterprise IT perspective, the organizational perimeter is no longer limited to a location. Now, it’s a set of dynamic-edge capabilities delivered from the cloud when needed.
Software-defined wide-area network (SD-WAN) deployments are skyrocketing around the world as enterprise organizations seek to connect people with applications and data from just about anywhere—putting SD-WAN security top of mind.
The assumptions underlying legacy WAN architectures—that most users work from branches, that almost everything lives in a central data center—no longer apply.1
This article explores:
Cyber risk at an all time high
While workplace flexibility and the acceleration of cloud-based application adoption offer new opportunities for organizations and their employees, they also present heightened security risks, with remote workers logging on from home or any public WiFi hotspot using a mixed bag of personal and company devices. At the same time—and not by coincidence—cyberattacks have become a more dangerous and imminent threat.
Within 18 months, 95% of enterprise businesses say their IT environment—including their infrastructure, applications and data analytics—will rely on the cloud.2
How SD-WAN enhances WAN security
SD-WAN offers many benefits to enterprise business, security among them. In contrast to traditional hub-and-spoke networks that route traffic through a centralized security inspection point, SD-WAN enables cloud-based firewalls and rule sets that help organizations apply the same security policies to all end users, regardless of location.
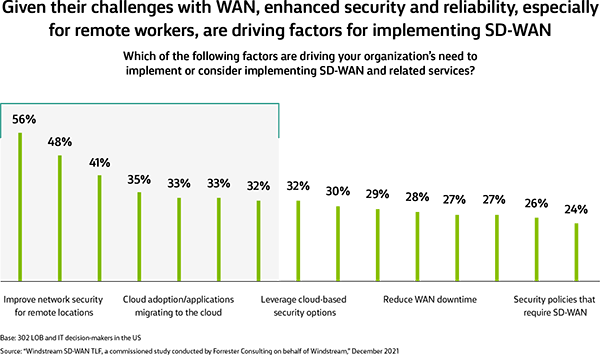
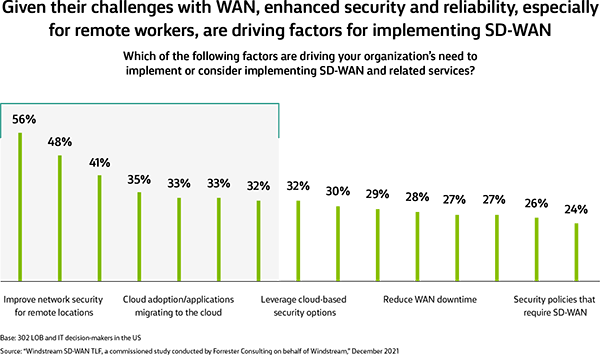
According to a recent study by Forrester Consulting, enhanced security and reliability, especially for remote workers, are key reasons for implementing SD-WAN.3
Security and reliability are driving factors for implementing SD-WAN
SD-WAN security features
| Is | Means |
|---|---|
| Dynamic IPSec deployment | SD-WAN protects traffic between locations by connecting them all with a secure tunnel that employs strong end-to-end encryption. |
| Centralized controller | Security is centralized and scalable via the SD-WAN controller. IT teams set policies and enforce them centrally. |
| Additional security functions | Many SD-WAN solutions come with stateful firewalls, and some offer basic VPN capabilities. |
SD-WAN security considerations
Data encryption and basic firewalls offer valuable layers of security, but today’s distributed network landscape often demands a more comprehensive approach. Cyberattacks, including ransomware, malware and distributed denial of service (DDoS), are growing in volume, sophistication and impact. In fact, according to SDxCentral, 86% of organizations expect to be impacted by a cyberattack within a year.4
And if organizations choose to deploy and manage SD-WAN on their own, the onus lands squarely on the IT teams to ensure security functions interoperate with other network components and protect critical business assets.
86% of organizations expect to be impacted by a cyberattack within a year.4
Maximize security with additional layers of protection
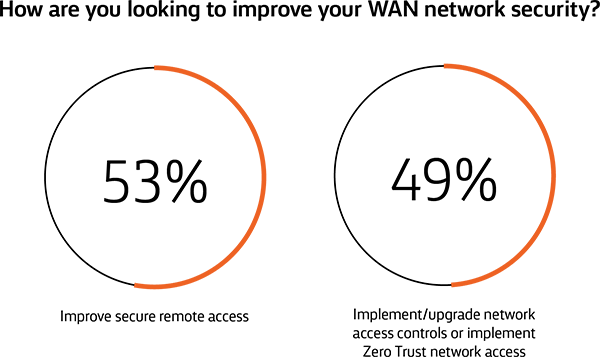
Improving network security is a top priority for today’s enterprise organizations. According to a recent Forrester Consulting study, roughly half of enterprise organizations are looking to improve secure remote access and implement or upgrade network access controls or implement Zero-Trust Network Access.3
Because most SD-WAN solutions don’t offer integrated next-generation firewalls and unified threat management (UTM) features out of the box, organizations often layer on additional security measures to protect against malware and data loss.
Consider managed network security
Some technology vendors offer complete, fully managed network security solutions—which might include firewall, intrusion prevention, security information and event management (SIEM), content filtering and application control—to complement and maximize SD-WAN security.
As a best practice for deploying SD-WAN, it’s essential to take stock of and assess your current environment, and plan forward to ensure you’re anticipating and getting ahead of evolving IT security requirements.
Improving network security is a top priority3
SD-WAN lays the foundation for SASE
To enable secure and reliable access to cloud-based assets, enterprises are increasingly turning to Secure Access Service Edge (SASE)—an emerging “as a Service” framework that builds on the strengths of SD-WAN. Coined by Gartner in 2019, SASE is the next evolution of the WAN that brings together networking and security into a centralized and centrally managed solution.
How SASE delivers secure anywhere, anytime access
SASE dynamically extends the edge of the private network right up to multiple clouds such as AWS, Azure and Google Cloud Platform and to popular SaaS applications.
For end users, this provides a virtual onramp to those cloud providers’ services. The computing and communications devices in the hands of those end users are also protected end-to-end by a full set of network security technologies. The policies for those technologies can be managed and orchestrated by the organization from the cloud using an intuitive self-service portal, reducing complexity and simplifying management.
The 5 components of SASE
SASE is more than a single technology: It’s a layered, interwoven fabric of network and security technologies that work together to protect an organization’s data and systems from unwanted access.
1. Software-Defined Wide-Area Networking (SD-WAN)
SASE is built upon a solid foundation of SD-WAN, intertwined with software intelligence, which enables optimal WAN management. SASE leverages SD-WAN capabilities to provide optimized application performance, network routing, global connectivity, WAN and Internet security, cloud acceleration, and remote access. SD-WAN also provides an ideal platform to secure unified communications applications, including voice, video and chat.
2. Firewall as a Service (FWaaS)
FWaaS is a new type of next-generation firewall. It eliminates the appliance form factor, making network security capabilities, such as URL filtering, available everywhere.
3. Secure Web Gateway (SWG)
SWG solutions protect users against malware, phishing and other web-borne threats. SASE offers SWG protection to all users at all locations and eliminates the need to maintain policies across multiple point solutions.
4. Zero-Trust Network Access (ZTNA)
ZTNA offers a modern approach to securing application access for users replacing legacy VPN. It embraces a zero-trust policy, where application access dynamically adjusts based on user identity, location, device type and more.
5. Cloud Access Security Broker (CASB)
CASB helps enterprises adapt and protect against new threats that come with cloud computing, like when connecting to IaaS and SaaS. CASB applies security policies as users access cloud-based resources to protect against cloud security risks, comply with data privacy regulations and enforce corporate security policies.
7 ways SASE benefits enterprise business
A robust SASE solution can not only positively impact your end users’ experiences, but also reduce your IT team’s management complexity and increase your organization’s bottom line.
Enterprise-level security that allows access to apps and data over any connection type.
Centralized operations that put policy management in the cloud and distributed enforcement points close to the user, app or device.
Device consolidation via the reduction of the amount of single-purpose customer premises equipment (CPE) at a branch to a single agent or SD-WAN device.
Secure access for remote workers that helps ensure encrypted connections and bases network access on the identity of the user, device or application—not an IP address or physical location.
Hybrid WAN that can run security over the top of both existing private MPLS connections and public Internet bandwidth for rapid, seamless deployment.
Improved performance which is critical for latency-sensitive apps such as collaboration, video, voice and web conferencing.
Lower operational overhead by eliminating the need for IT to constantly update, patch and scale appliances.
Is SASE right for your business?
If these trends and challenges apply to you, a SASE solution may be right for your organization:
Common SASE use cases
- Need protection from malware and exposure to security vulnerabilities
- Disjointed management of siloed security and networking technologies
- Applications reside in the cloud
- End users connect to your network from outside a controlled environment
- Limited visibility to cloud compute and end-user resources
- End-user performance experience is degrading
- Unable to control all device connections to your network
- Increased network complexity
- End users expect more direct access to resources
64% of businesses are adopting or plan to adopt SASE in the next year.5
When to work with a managed service provider
SASE includes new security capabilities that require a specialized skill set and operational management—and security professionals are in high demand but short supply.
Nearly half of respondents in a recent Forrester Consulting study say that designing, deploying and managing a dispersed set of security functions would be/is a challenge in their SD-WAN adoption.3
When thinking about SD-WAN and SASE, consider whether a single managed service provider—one who offers all components of a SASE stack—might fill an expertise or resourcing gap and alleviate some of the management complexity that would otherwise reside solely with the network and security teams. If your teams’ resources are concentrated on other top-level priorities, it may be wise to leverage a provider.
What to look for in a managed SASE provider
Standing up a SASE solution isn’t like flipping a switch, and not all vendors are created equal. Organizations may be limited by legacy network and security point solutions, or their provider’s capabilities and readiness to deploy SASE technologies. Barriers to adoption may include:
Vendor focus
Your provider’s capabilities and offerings may be focused exclusively on networks or on security, but it’s possible they aren’t proficient in both areas.
Vendor approach
Well-integrated features, in-line proxy experience and context awareness are all key to successful SASE implementation. If a vendor lacks them, it can increase costs and decrease performance.
Vendor history
Your provider’s legacy experience may be with on-premises hardware in the “data-center-centric” approach, which can create resistance to a cloud-native mindset.
Security challenges top of mind for enterprise business3
SD-WAN security and the SASE future
Enterprise business today demands effective management of both networking performance and security, regardless of where users connect from—and SD-WAN sets a strong foundation.
More than 4,000 enterprises trust Windstream Enterprise to enhance network resilience and optimize application performance, while accelerating cloud adoption at more than 32,000 of their critical locations. Windstream Enterprise has partnered with the leading SD-WAN architecture providers—Fortinet® and VMware—to offer you a choice in technology platforms. Check out this collection of SD-WAN case studies to see how we’ve helped clients transform their networks.
Windstream Enterprise is also the first and only North American managed service provider to converge cloud-native network and security into a fully integrated SASE solution in partnership with Cato Networks. This comprehensive architecture enables businesses to adapt to constantly shifting users, applications and work environments, while keeping all application and security policies synchronized with these changing endpoints—all from a single pane of glass.
With our experience in providing all the foundational elements of a robust SASE solution, you can count on Windstream Enterprise to continue developing our SASE expertise, capabilities and solution offerings.
Want to compare security functions?
Download this SD-WAN Security Checklist for a side-by-side comparison of SD-WAN security, Managed Network Security and SASE.
Sources
- SASE & ZTNA for Dummies: VMware Special Edition. For Dummies. 2021.
- “2020 Cloud Computing Study.” IDC. July 8, 2020.
- Shift Your Network Thinking to SD-WAN. A Forrester Consulting Thought Leadership Paper Commissioned By Windstream. January 2022.
- Lui, Nancy. Trend Micro. SDxCentral. August 2021. Accessed January 18, 2022.
- 2021 Strategic Roadmap for SASE Convergence. Gartner. March 2021. Accessed January 18, 2022.