How to implement a SASE framework in your organization
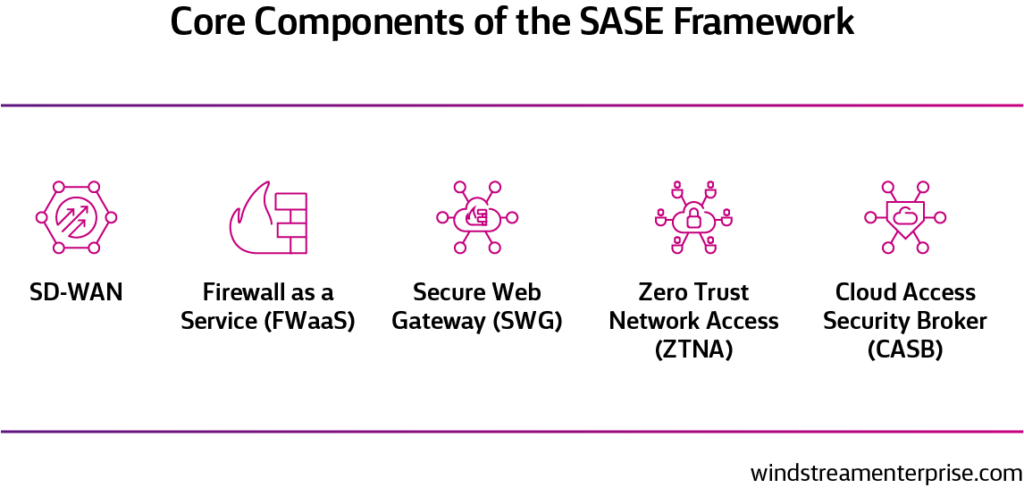
As the cloud era continues to redefine the business network, SASE (through its five core components) will enable organizations to deliver protected networking and security services for greater workforce mobility.
To implement a SASE framework in your organization, a step-by-step approach is encouraged.
Step 1: Plan your project
Defining the business goals your SASE will address and assessing what elements you’ll need are critical to launching your SASE framework. Consider what technology, processes and training are required to ensure successful implementation.
Step 2: Review what you have and what you need
Take a hard look at your existing network and infrastructure, including staff who work with them, and identify gaps that need to be addressed. A clearer understanding of these pieces will help you choose solutions that will benefit your organization most.
Step 3: Choose the right solutions (and vendors to supply and support them)
To implement a SASE solution, you’ll need an SD-WAN backbone that provides all networking functionality (including security) or a combination of SD-WAN and a Security Service Edge (SSE) solution that provides the same cloud-based security edge features. Since all SASE components need to work well together, be sure to prioritize integration when evaluating potential vendors.
Step 4: Stage, test and troubleshoot
Creating a staging and testing environment separate from the production environment is highly recommended before going live with a SASE deployment. It will allow for thorough integration and user acceptance testing as well as troubleshooting for any issues that arise without negatively affecting business operations.
Step 5: Monitor and optimize SASE as needed
With any successful SASE implementation, it’s important to monitor how it is being used and look for ways to improve and optimize. As infrastructures evolve, technology improves and your business grows, remember to evaluate regularly to see if additional functionalities could be added to your SASE framework.